It’s safe to say that the one of the dominating IT-trends over the next years will be the internet of things (IoT). The IoT by definition encompasses any device which can be connected to the internet. That could be any device, ranging from wending machines to wearables and all smart home devices, such as lamps, routers or IP cameras. The term IoT is frequently also used when referring to components of a machine, such as car engines, or the drill of an oil rig. For businesses, this trend could potentially drive a major increase in productivity as more and more processes are fully digitalized. Equally, the smart home could lead to a significant change in how consumers interact with electronic devices. While most observers agree that both trends pave the way towards a new industrial revolution, recent incidents also show that security is a major concern for smart devices. Contrary to what most media reports suggest, however, the threat lies not in attackers taking over your smart home or sabotaging the digital factory. While those threat do exist, the real issues will not be affecting most consumers or business directly, but are nevertheless equally dangerous to the economy.
The general issue with smart devices is the fact that their technology often relies on outdated software, vulnerable operating systems or that obsolete cryptography is used and weak authentication mechanisms are implemented. There are several reasons for that. One, for example, is the increasing pace of technological advancement. Applications considered secure just a few years back are riddled with vulnerabilities today. Also, consider the costs for smart devices. Smart devices, in order to boost productivity as planned need to be commodities, produced in high volumes – from an economical perspective, it’s simply not feasible to provide security updates for a long period of time, if at all. Lastly, there is simplicity. A sophisticated security concept makes sense for critical systems, such as Enterprise Resourse Planning (ERP) systems, but a sensor should be easy to administrate. Combine those things and you have a security nightmare right there.
Will the world economy, therefore, be put in danger if future burglars will enter our homes using a laptop rather than a crowbar? Or if an industrial robot is used to transfer a company’s revenue to an offshore account? While that is certainly possible, the real danger lies in smart devices being misused for other purposes. Case in Point: the Mirai botnet which left much of the internet inaccessible on the U.S. east coast in October 2016. Back then, a massive Distributed Denial of Service (DDoS) Attack was responsible for most of the major US websites not being reachable anymore. Technically, thousands, even millions of computers were bombarding those websites at the same time – resulting in their servers overreaching their capacity and subsequently surrendered to the unexpected amount of traffic. The surprising fact about that particular botnet was that it consisted of said smart devices rather than captured “regular” PCs or servers. In other words, it was vending machines, security cameras and baby monitors that brought down Google, Facebook and others on that bright October day in 2016.
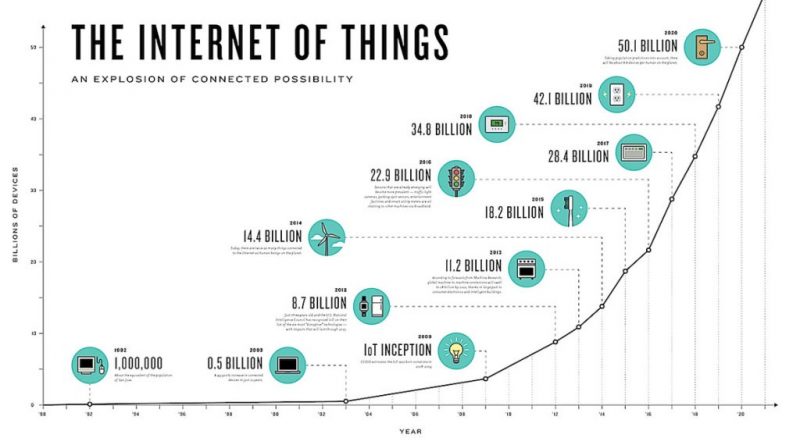
The Mirai Botnet examples pinpoints the real danger in IoT security concerns. Most people don’t think of IoT devices as being computers, but they nevertheless have certain processing powers and are connected to the internet. Due to the fact that – for the reasons mentioned earlier – security updates are rare for those kind of devices, they become a welcome target for botnet builders. Let’s take a look at the numbers: in 2017 there were an estimated1 8.4 billion of those devices online, with the number almost tripling by 2020 to reach more than 20 billion. Now map those numbers to other criminal cyber activities. Think click fraud, where botnets generate false revenue for internet ads, or crypto mining, where botnet devices are used for generating digital money. Cyber criminals are creative, and they will surely find a way to take advantage of that vast amount of resources to their disposal.
How can those criminal activities prevented and a higher standard of security enforced, then? The answer is obvious: enforce security standards and security updates for IoT devices. However, achieving this will take a considerable amount of time, as another example in IT security shows: HTTPS (Hypertext Transfer Protocol Secure) was introduced in 1994 by Netscape2 . But only now, 24 years later, beginning this month (July 2018) with the release of Chrome 68, Google Chrome will start marking all non-HTTPS pages as “not secure”3. Let’s hope IoT security standards will pick up faster than that.

1https://www.gartner.com/newsroom/id/3598917
2https://en.wikipedia.org/wiki/HTTPS
3https://security.googleblog.com/2018/02/a-secure-web-is-here-to-stay.html
Patrick Boch has been working in the IT industry since 1999. He has been dealing with the topic of cybersecurity for several years now, with a focus on SAP and ERP security.
In recent years, Patrick Boch has published various books and articles as an expert, especially on the subject of SAP security. With his extensive knowledge and experience in the areas of SAP compliance and security, Patrick Boch has served as product manager for several companies in the IT security sector since 2013. Patrick is Co-Founder and Editor of Cyber Protection Magazine.



I’ll be interested in what is presented at embedded world on the subject
Pingback: Boost Your Smart Devices Security this Holiday Season