The growing number, complexity, and diversity of network attacks as well as sophistication of modern malicious software and tools used for this purpose urge the security community to seek for other, promising directions which cybersecurity research and development should follow. We are currently in the state where current countermeasures are progressively showing their limitations and are unable to completely cope with new waves of threats – consider, for example, the recent plague of ransomware. Thus, we believe that it is now time for security professionals and researchers to turn to nature in the search for inspirations for the next-generation defense systems.
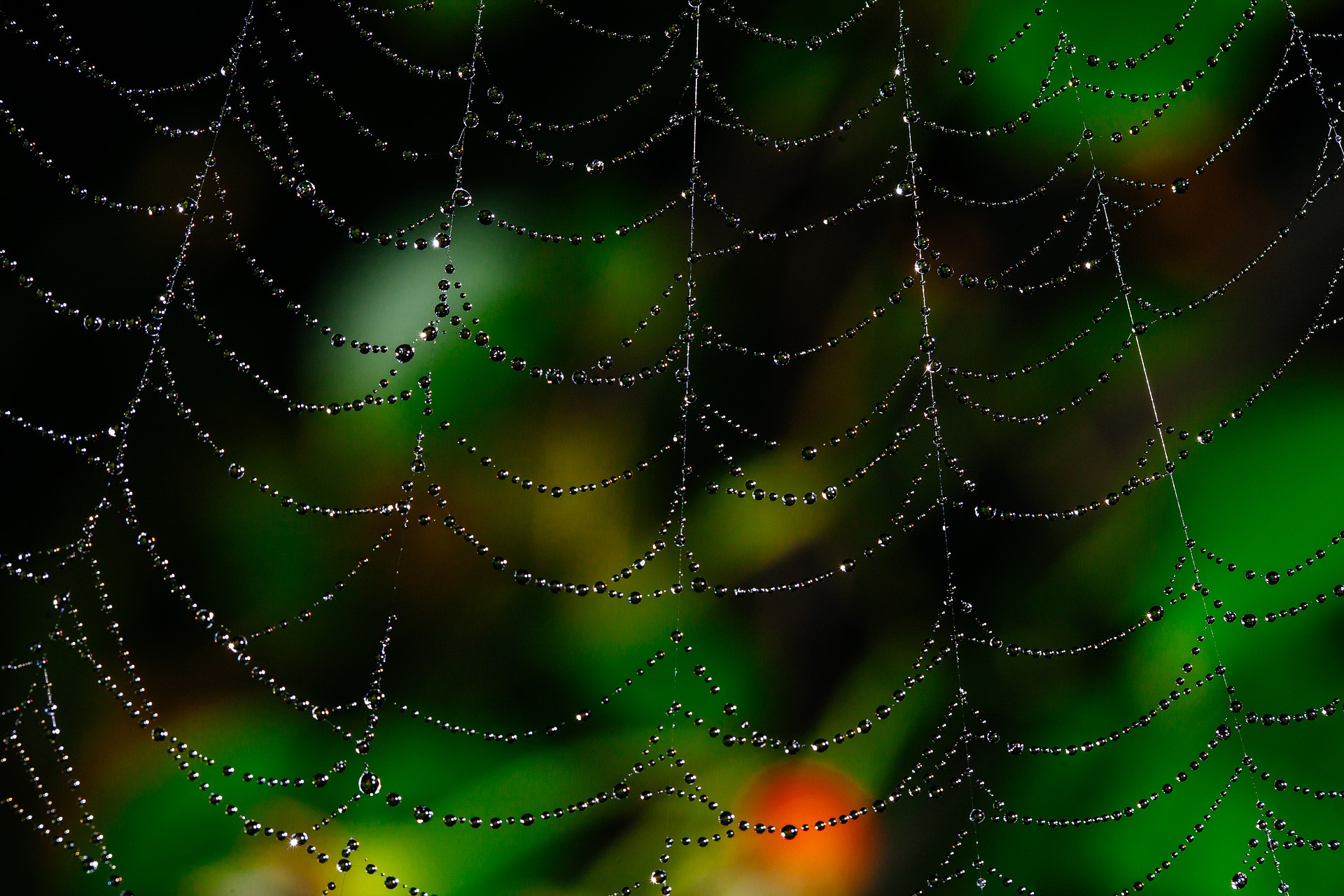
Humankind has a very rich history of benefiting from the nature-based inspirations. Many every day inventions that are today obvious have their roots in biomimicry. Consider, for example, Velcro which is a fabric hook-and-loop fastener that was invented by closely inspecting burdock burrs. The other example could be fast swimming suits which have fabric that replicates a shark’s dermal denticles to reduce drag and helped break a few world records. Success of these and many, many more bio-inspired inventions is not surprising since nature has over three billion years of experience in evolution of various types of organisms and adapting them to the diverse environmental conditions.
In the Internet it has been already discovered that many currently used offensive and defensive solutions (unconsciously) mimic the ongoing arms race between various species in nature. Moreover, many of the virtual world’s current network attacks are nothing new. Worms, spam campaigns, botnets, and so on, along with defensive techniques such as firewalls and Intrusion Detection/Prevention Systems (ID/PSs), have been found to have counterparts in nature [1].
Considering above the obvious question arises: why cannotwe directly benefit from the nature’s solutions in cybersecurity, too?
First of all, it must be noted that we have been already on the right path once: first generation cybersecurity solutions were in fact bio-inspired e.g. the human immune system inspired threat detection based on the signature analysis [2]. However, since then the threats have evolved significantly to make these first-generation defenses less effective. And what is worse we ceased to follow the biomimicry path – we ceased to evolve fast and effective enough. Therefore, in order to “survive”, cybersecurity defenses must be adapted, using nature-based inspiration, to be able to efficiently counter the new threats. Fortunately, a next generation of bio-inspired cybersecurity research is now emerging (see e.g. recent detection systems borrowing inspirations from ants [3] or bees [4] behavior); however, we find also that the knowledge and achievements are scattered because the field lacks a more general framework and more general overview.
Moreover, future network defenses should seek for the nature-based inspirations using two potential paths. The first is to draw inspirations from the particular organism’s characteristic feature/defense mechanism. For example, such features like aposematism (warning signal that is associated with the unprofitability of a prey item to potential predators) or autotomy (where an animal sheds or discards one or more of its own body parts to elude or distract the predator) could easily become an inspiration for the next-generation cybersecurity solutions. Another potential approach is to closely investigate also nature-based interactions. As already observed in [5] the malware-host scenario bears many similarities to parasite-host one, thus, research attention could be directed to the biology models and achievements in this field.
Obviously, the mappings from nature to the cyber world will be not faithful copies as exact mappings are not realistic in practice. Nevertheless, we believe that drawing inspirations from the organisms’ characteristic features or defense mechanisms is a must and considering the pace at which new threats are evolving it is even more urging necessity than before.
References
- [1] W. Mazurczyk, E. Rzeszutko. Security – a perpetual war: lessons from nature. IEEE IT Professional, vol. 17, no. 1, pp. 16-22, January/February 2015
- [2] S. Forrest, S. A. Hofmeyr, A. Somayaji. Computer immunology. Communications of the ACM 40 (10), 88-96, 1997
- [3] G.A. Fink, J.N. Haack, A.D. McKinnon, E.W. Fulp. Defense on the Move: Ant-Based Cyber Defense. Security & Privacy, IEEE , vol.12, no.2, pp.36,43, Mar.-Apr. 2014
- [4] M. Korczynski, A. Hamieh, J. H. Huhx, H. Holmy, S. R. Rajagopalanx, N. H. Fefferman, Hive Oversight for Network Intrusion Early-warning using DIAMoND (HONIED): A bee-inspired method for fully distributed cyber defense, IEEE Communications, June 2016
- [5] W. Mazurczyk, S. Drobniak, S. Moore. Towards a Systematic View on Cybersecurity Ecology. B. Akhgar and B. Brewster (eds.), Combatting Cybercrime and Cyberterrorism, Advanced Sciences and Technologies for Security Applications, Springer, DOI: 10.1007/978-3-319-38930-1, June 2016, pp. 17-37
Wojciech Mazurczyk
Wojciech Mazurczyk holds D.Sc. (habilitation, 2014) and Ph.D. (2009) in telecommunications (with honours) from Warsaw University of Technology, Poland.
Associate Professor at Department of Cybersecurity, Institute of Telecommunications, Faculty of Electronics and Information Technology, Warsaw University of Technology. A member of the Parallelism and VLSI Group at Faculty of Mathematics and Computer Science at FernUniversitat, Germany
Author or co-author of 2 books, over 120 papers, 2 patent applications and over 35 invited talks. Involved in many international and domestic research project as a principal investigator or as a senior researcher. A guest editor of many special issues devoted to network security (among others: IEEE TDSC, IEEE S&P, IEEE Commag). Serving as Technical Program Committee Member of (among others): IEEE INFOCOM, IEEE GLOBECOM, IEEE ICC, IEEE LCN, IEEE CNS, IEEE WIFS and ACM IH&MMSec. From 2016 Editor-in-Chief of an open access Journal of Cyber Security and Mobility.
An Accredited Cybercrime Expert and Trainer for Europol EC3 (European Cybercrime Center). A founder and a coordinator of the Criminal Use of Information Hiding (CUIng) Initative launched in cooperation with Europol EC3. A founding member of EURASIP “Biometrics, Data Forensics and Security” (B.For.Sec) Special Area Team. IEEE Senior Member (2013-) and EURASIP member (2015-). Involved in the think thank of FP7 project CAMINO (Comprehensive Approach to cyber roadMap coordINation and develOpment) (2015-).
For over 10 years has been serving as the independent consultant in the fields of network security and telecommunications. Between 2003 and 2007 he was also a deployments specialist for the telecom company Suntech.
His research was covered by worldwide media numerous times including in “IEEE Spectrum”, “New Scientist”, “MIT Technology Review”, “The Economist”, “Der Spiegel”, etc.


Leave a Reply