The internet of things (IoT) is the convergence of connecting people, things, data and processes; it is transforming our life, business and everything in between. In his book, “Secure and Smart IoT”, Prof. Ahmed Banafa explores many aspects of the IoT and explains many of the complicated principles of IoT and the new advancements in IoT including Fog Computing, AI and blockchain technology.
We had the chance to interview Prof. Banafa on his book, which just recently won the Annual Author & Artist Award of 2019 from San Jose State University. In the first part of this interview, Prof. Banafa elaborates on what the IoT will mean for the future and how this relates to security. The second part of the interview will then focus on how blockchain, fog computing and AI will help manage the complexity of the IoT.
Cybersecurity Magazine: What can we expect from the growth of IoT in the near future?
Prof. Banafa: By 2020, the Internet of Things (IoT) is predicted to generate an additional $344B in revenues, as well as to drive $177B in cost reductions. IoT and smart devices are already increasing performance metrics of major US-based factories. They are in the hands of employees, covering routine management issues and boosting their productivity by 40-60% .
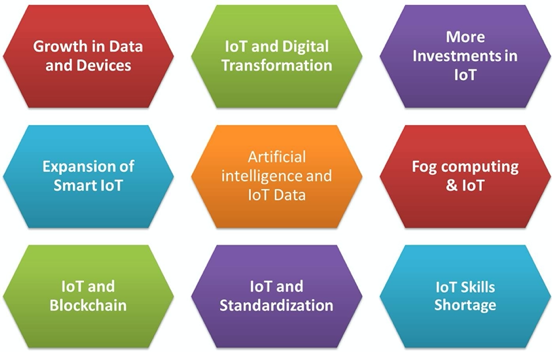
The following list of predictions (Figure 1) explores the state of IoT in 2019 and covering IoT impact on many aspects business and technology including Digital Transformation, Blockchain, AI, and 5G :
- Growth in Data and Devices
- IoT and Digital Transformation working well
- More Investments in IoT
- Expansion of Smart IoT
- Artificial Intelligence and IoT Data analytics
- Fog Computing & IoT
- IoT and Blockchain for security
- IoT and Standardization is reality
- IoT Skills Shortage continte
Source: https://www.linkedin.com/pulse/nine-iot-predictions-2019-ahmed-banafa/
CSM: What are the most imminent security threats for the IoT – especially considering that most devices are not sufficiently secured?
Prof. Banafa: The concept of IoT introduces a wide range of new security risks and challenges to IoT devices, platforms and operating systems, communications, and even the systems to which they’re connected. New security technologies will be required to protect IoT devices and platforms from both information attacks and physical tampering, to encrypt their communications, and to address new challenges such as impersonating “things” or denial-of-sleep attacks that drain batteries, to denial-of-service attack (DoS). But IoT security will be complicated by the fact that many “things” use simple processors and operating systems that may not support sophisticated security approaches.
This fear was realized with a massive distributed denial of service attack that crippled the servers of services like Twitter, NetFlix , NYTimes, and PayPal across the U.S. on October 21st , 2016. It’s the result of an immense assault that involved millions of Internet addresses and malicious software, according to Dyn, the prime victim of that attack. “One source of the traffic for the attacks was devices infected by the Mirai botnet” the link to the source code of Mirai malware on GitHub .The attack comes amid heightened cybersecurity fears and a rising number of Internet security breaches. Preliminary indications suggest that countless Internet of Things (IoT) devices that power everyday technology like closed-circuit cameras and smart-home devices were hijacked by the malware, and used against the servers.
What makes this attack so interesting is that the devices hijacked have been networked to create the internet of things. In this case the offender was likely digital video recorders, those set-top boxes that allow you to record live TV and skip the commercials, and webcams, like those used around houses for security. All these devices now moonlight as zombies under control of malicious actors bent on taking down individual websites or even portions of the internet, as with the Dyn attack.
CSM: What about privacy – can the different privacy requirements for different countries be brought together?
Prof. Banafa: This is part of a standardization process which is difficult. As the industry evolves, the need for a standard model to perform common IoT backend tasks, such as processing, storage, and firmware updates, is becoming more relevant. In that new model, we are likely to see different IoT solutions work with common backend services, which will guarantee levels of interoperability, portability, and manageability that are almost impossible to achieve with the current generation of IoT solutions.
Creating that model will never be an easy task by any level of imagination, there are hurdles and challenges facing the standardization and implementation of IoT solutions and that model needs to overcome all of them.
CSM: What does the emergence of 5G mean for the IoT?
Prof. Banafa: By the end of this year there will be are around 3.6 billion devices that are actively connected to the Internet and used for daily tasks according to IT Pro [8]. With the introduction of 5G that will open the door for more devices, and data traffic. You can add to this trend the increase adoption of edge computing which will make it easier for business to process data faster and close to the points of action.
This article is the first part of the interview with Prof. Banafa – the second article will be published shortly.
Prof. Ahmed Banafa
Prof. Ahmed Banafa has extensive research work with focus on IoT, Blockchain, cybersecurity and AI. He served as a faculty at well-known universities and colleges.
He is the recipient of several awards, including Distinguished Tenured Staff Award, Instructor of the year and Certificate of Honor from the City and County of San Francisco.
He was named as No.1 tech voice to follow by LinkedIn (with 38k+ followers ), featured in Forbes, IEEE-IoT and MIT Technology Review, with frequent appearances on ABC, CBS, NBC, BBC and Fox TV and Radio stations.
He studied Electrical Engineering at Lehigh University, Cybersecurity at Harvard University, and Digital Transformation at MIT.


Leave a Reply