The field of telecommunications in general, and mobile network security in particular, is a prime example for the importance of technical standards – binding rulesets serving as one of the cornerstones of a globalized society. Without these agreements in place, ubiquitous use cases like roaming into foreign mobile networks would be completely out of question, as they determine the fundamental components and procedures required for interoperability.
However, in their general applicability also lies an inherent limitation of international mobile standards: They usually do not go into great detail and anything solely concerning communication within a single entity’s security domain can hardly be mandated. Moreover, geopolitical and regulatory factors rule out the definition of one single definitive 5G security. Hence, mobile specifications by 3GPP always contain a certain degree of optionality. This is where individual mobile operators have to take informed decision on the security baseline of their services and enforce network-wide policies accordingly.
In this article, we will highlight some of the optional features and parameters with regards to 5G security and explore how 5G operators can utilize them to provide their subscribers the most secure service while simultaneously establishing a competitive edge over their competitors.
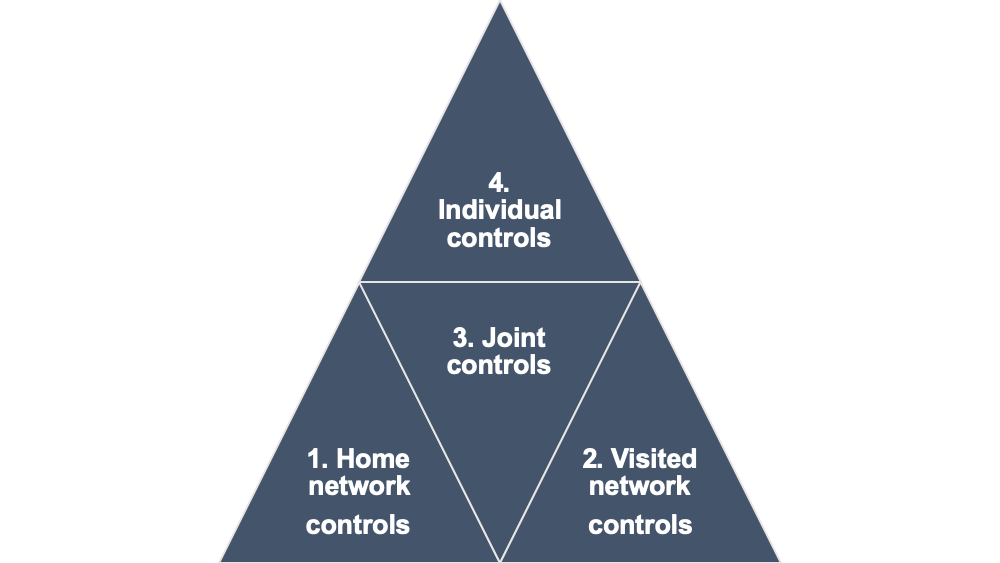
1. Security options under control of the home network operator
The first category comprises security parameter that are solely controlled by the home network operator. As gatekeeper of the subscriber’s authentication credentials, these controls are mostly related to the authentication procedure, i.e. confidentially validating the identity of a subscriber from network side and vice-versa.
For the very first time, 5G allows avoiding to transmit the subscribers permanent identity by encrypting this information. For this to happen, home network operators need to explicitly enable the feature by setting the respective configuration flag in the SIM card. One can choose to perform the encryption of the Subscription Permanent Identifier (SUPI), resulting in the Subscription Concealed Identifier (SUCI), either in the mobile device or in the SIM itself. The former option only allows operators to indicate the priority of standardized concealment algorithms to be used by the handset via the SIM card. The latter option may be of interest for operators that either wish to make use of non-standard concealment algorithms, or do not want to rely on each individual handsets’ implementation. At the same time, working with one single implementation of the cryptographic primitives can help to reduce test efforts for new mobile devices. It should be noted that any concealment algorithm used on the device side also has to be supported by the core network function in charge of deconcealing the SUCI.
Another option is relevant for the prevention of fraudulent requests by foreign networks. Key enabler for this new feature is the 5G Authentication Server Function (AUSF) in visited networks which is required to report the result of each authentication run to the home network of the subscriber. In turn, it is in the home networks control to utilize this notification. Storing information –such as visited network name or timestamp of latest successful authentication– and based on it taking decisions on whether to allow subsequent procedures allows the home network to prevent specific types of fraud.
2. Security options under control of the visited network operator
The second type of controls we want to focus on concerns security options under control of the visited network operator. Depending on whether a subscriber is currently roaming or not, this may be equal to the home network operator.
Since the visited network determines the algorithms used to protect integrity and confidentiality on the air interface, it should enforce the use of secure algorithms. This means defining a priority of algorithms to be used and explicitly disabling use of the ones that do not offer effective protection for any use cases other than emergency calls. However, note that regulatory agencies in certain countries do not allow disabling these so-called NULL algorithms.
Aside from the air interface, it is on the visited network to enforce protection on the links connecting individual radio network nodes as well as the access and core network. This may be realized using either IPsec or DTLS. The certificate enrolment mechanism for base stations specified in 3GPP’s Technical Specification 33.310 can be helpful for provisioning radio network elements with the required cryptographic material for these security protocols.
The visited network also assigns a temporary identifier to each subscriber. The so-called 5G Globally Unique Temporary Identity (5G-GUTI) is used to identify the mobile handset in lieu of the SUPI so it is not ever required to send the latter over the air. Failing to regularly reassign a 5G-GUTI after a certain amount of time defeats the purpose of a temporary identity and may lead to privacy issues for the subscriber.
In order to verify the identity of an already registered subscriber, another good practice is to regularly trigger a reauthentication with the home network. In addition to authenticating the subscriber at the time of initial attach, running this procedure again creates more confidence in its identity and refreshes the security context. In case an operator manages both 5G and earlier generation networks, it is also advisable to force reauthentication after an inter-radio technology handover. Even though 5G only allows direct handover from 4G/LTE, this in turn may be connected to UMTS or GSM networks. Allowing subscribers to move between those security domains without reauthentication needs to be prevented.
The visited network also decides how subscribers are handed over to and from a particular base station depending on its security characteristics. For example, a certain high-security area might be served by a specific AMF with different cryptographic requirements to protect signaling traffic. In that case, the operator can choose to force handovers via N2 interface (i.e. incl. AMF change) simultaneously resulting in the derivation of fresh cryptographic keys for the radio access network.
3. Security options to be agreed between home and visited network operator
5G also features a few security options that require both the home and visited network operator to agree upon, since the newly defined signaling protocol offers roaming partners fine-grained control over what information to protect on the interconnect between them. While the 3GPP specification mandates a few crucial data points to be protected at any time, applying the same policy to the remaining data is not compulsory. This also includes the aforementioned permanent subscription identity (SUPI). Hence, operators aiming to achieve the maximum level of security and privacy for outbound and inbound roamers should mandate in their roaming agreements that as much information as possible is to be transferred in a protected manner. Extending on that, if operators do not necessarily depend on exchange providers to access contents of the signaling data between them and their roaming partners (e.g. for the purposes of alleviating incompatibilities between them), there is also the option to use TLS on the interconnect. This should be the preferred way of integration since it offers end-to-end protection for the complete communication.
4. Security options under individual control of both home and visited network operator
Lastly, some of the optional 5G security controls concern both the home network and the visited network operator equally. These mostly relate to general network security recommendations 3GPP is hinting to in its specification but does not mandate, such as enforcing integrity protection, confidentiality protection as well as explicit authentication between network elements by means of IPsec or DTLS. Without the use of these security protocols internal to an operator’s network, one could argue that protection is provided implicitly. After all, the whole network is owned and controlled by a single entity that has trust in its infrastructure, right? This may have been a reasonable premise in previous generations, but with 5G putting heavy emphasize on virtualized deployments and edge computing blurring the lines of ‘trusted’ vs. ‘non-trusted’ environments, this rationale is crumbling.
In addition to that, 3GPP Technical Specification 33.210 aims to provide best practices for profiling security protocols, such as IPsec and DTLS. Following this guidance, but also disabling any other weak profiles is key for effective security assurance. As most network vendor’s solutions support a wide range of security algorithms, making an informed decision on what to explicitly disable is vital.
In this article, we discussed optional security features and parameters included in 3GPP’s 5G specification and provided some guidance on how to configure them. Needless to say, solely following the standards is far from enough. These documents cannot serve as a comprehensive manual for operating a secure mobile network. But understanding the nuances of 5G security and configuring it according to one’s requirements is essential to make the most of this solid foundation.
Hans Christian Rudolph
Experienced security professional in the field of telecommunications. Fortunate to have been involved in both in3GPP standards development as well as in building real-world mobile networks from scratch. Currently focussed oncore network security, roaming security and fraud prevention.



Leave a Reply