This article is a result of me hearing this sentence uttered in a serious setting:
‘We do not need networking or network security; we have all of our infrastructure in the cloud.’
This provoked me somewhat, since I disagree with everything in the above sentence. The network and network security have never been more important, especially since much of our earlier on-prem infrastructure is now running in the cloud. I have personally had clients that have used developers to create a new CMS on one of the big cloud vendors, with the result that the infrastructure the CMS was using all ran in the same VLAN with full access between the various servers and no thought to the design of the underlying network or the security needed for the virtual network.
The client’s thinking was that cloud was software, so a developer was enough to create the new CMS. Suffice to say the assessment I was hired to perform on the new CMS resulted in the client having to scrap the implementation and recreate it with proper design on the network layer and implementation of security at this same layer.
Yes, network security is crucial when using cloud services. Cloud computing involves storing and processing data on remote servers that are accessible over the internet. As a result, it’s important to ensure that the data and applications hosted in the cloud are secure and protected against unauthorized access or attacks.
Key considerations for multi-cloud deployments
Most of the clients I am interacting with daily are using more than one cloud vendor. Network security in a multi-cloud setting is even more important than in a single cloud environment because it involves managing security across multiple cloud platforms. Here are some key considerations for network security in a multi-cloud environment:
- Centralized management: A centralized management approach can help ensure consistent security policies and configurations across all the cloud platforms. This can be achieved through tools such as a Security Information and Event Management (SIEM) system or a cloud security platform that integrates with multiple cloud providers.
- Segmentation: Segmenting networks in a multi-cloud environment can help reduce the attack surface and limit the impact of a security breach. This can be achieved through tools such as Virtual Private Clouds (VPCs), which provide isolation between different cloud resources and allow for the creation of separate network segments.
- Access control: Access control is critical in a multi-cloud environment to ensure that only authorized users and devices have access to cloud resources. This can be achieved using multi-factor authentication, role-based access control, and other access control mechanisms.
- Encryption: Encryption can help protect data as it moves between different cloud providers and as it’s stored in the cloud. This can be achieved using Transport Layer Security (TLS) and other encryption protocols.
- Monitoring and logging: Monitoring and logging can help detect security incidents and provide visibility into the security posture of the multi-cloud environment. This can be achieved through tools such as SIEM systems, which can consolidate logs and events from different cloud providers.
See the figure below:
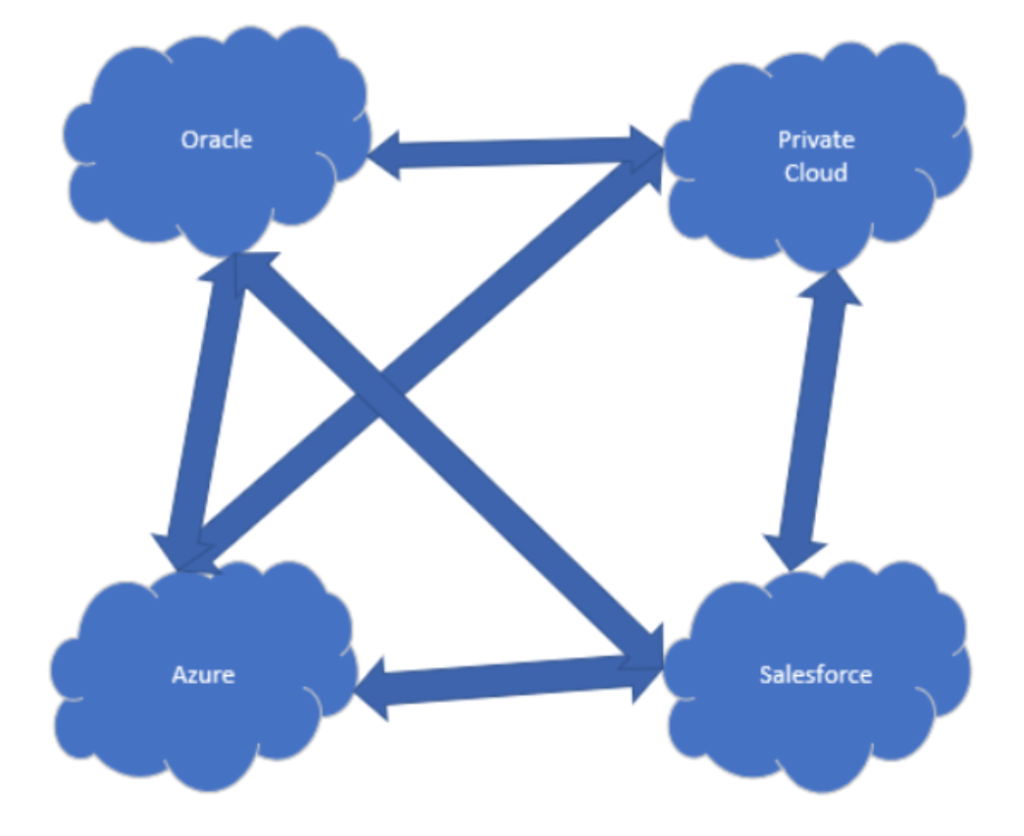
Network security and traffic control are vital in the above setting. If there are applications that are running on top of multiple different cloud vendors, this importance is only increasing, especially if the application and its data a critical to the business environment.
Key considerations for Infrastructure-as-a-Service
I would argue that network security is important in SaaS and PaaS services as well, but here I will elaborate on the IaaS case. In an Infrastructure-as-a-Service (IaaS) setting, network security is essential for protecting the underlying infrastructure, applications, and data hosted on the cloud. Here are some key considerations for network security in an IaaS setting:
- Firewall protection: A firewall can be used to restrict traffic to and from the IaaS infrastructure. This can be achieved using network security groups, which can be configured to allow or deny traffic based on a set of rules.
- Access control: Access control is critical in an IaaS environment to ensure that only authorized users and devices have access to cloud resources. This can be achieved using multi-factor authentication, role-based access control, and other access control mechanisms.
- Encryption: Encryption can help protect data as it moves between different cloud providers and as it’s stored in the cloud. This can be achieved using TLS and other encryption protocols.
- Network segmentation: Segmenting networks in an IaaS environment can help reduce the attack surface and limit the impact of a security breach. This can be achieved through tools such as VPCs, which provide isolation between different cloud resources and allow for the creation of separate network segments.
When adding the consideration that an on-prem networking infrastructure is important for accessing the cloud, I should think that the network and network security is becoming an even more critical component for any business, not less of one.
See the figure below:

Source: File:Cloud computing.svg – https://en.wikipedia.org
Considering the number of devices that can be used to access critical cloud resources, as well as the fact that not all these devices are under the control on the business/organization, the only way we can exercise any form for control on what the devices are doing, is the network layer.
Security at the network layer is essential for protecting data and preventing unauthorized access to network resources. With zero-trust becoming more and more important in many organizations, skipping out on security at the networking layer is a monumental mistake to my mind, since the networking layer is the foundation for all of the various zero-trust steps above.
Tom Madsen
Tom Madsen has been active in the cybersecurity industry for more than 20 years. Tom graduated from the University of Aalborg and covered several technical roles in security during his professional career. He is certified as CISSP, CISA, CISM, CGEIT, CRISK, CCSP, CDSPE and CSSLP, and has published the book “The Art of War for Cybersecurity”. He is currently writing a book ‘Security Architecture – How & Why’.



Leave a Reply